
What is HEXNULL and Why Autonomous Security Needs Architecture
Introduction Autonomous security is not a feature. It is not a chatbot wrapper around nmap.It is not an LLM summarizing
Autonomous security is not a feature.
It is not a chatbot wrapper around nmap.
It is not an LLM summarizing scan results.
It is not a prompt chained to a vulnerability scanner.
Autonomous security is an architectural problem.
HEXNULL exists to address that problem.
I build AI agents for penetration testing workflows, recon automation tools, CVE contextualization, log triage systems, and offensive security automation — but always through structured architecture.
This article explains:
This is not about replacing security engineers.
It is about augmenting them with engineered intelligence.
HEXNULL is not a company.
It is not a hacker persona.
It is not an underground tool vendor.
HEXNULL is a pseudonymous independent AI Agent Architect focused on offensive security automation.
The core mission:
Design structured AI systems that operate inside penetration testing workflows.
The emphasis is deliberate:
HEXNULL is not about building more scripts.
It is about building agent architectures.
Most current “AI security tools” fall into three categories:
These are tools.
They are not agents.
An agent must:
Most AI security products do none of these.
They execute.
They do not reason.
And most importantly — they lack architecture.
Most current “AI security tools” fall into three categories:
These are tools.
They are not agents.
An agent must:
Most AI security products do none of these.
They execute.
They do not reason.
And most importantly — they lack architecture.
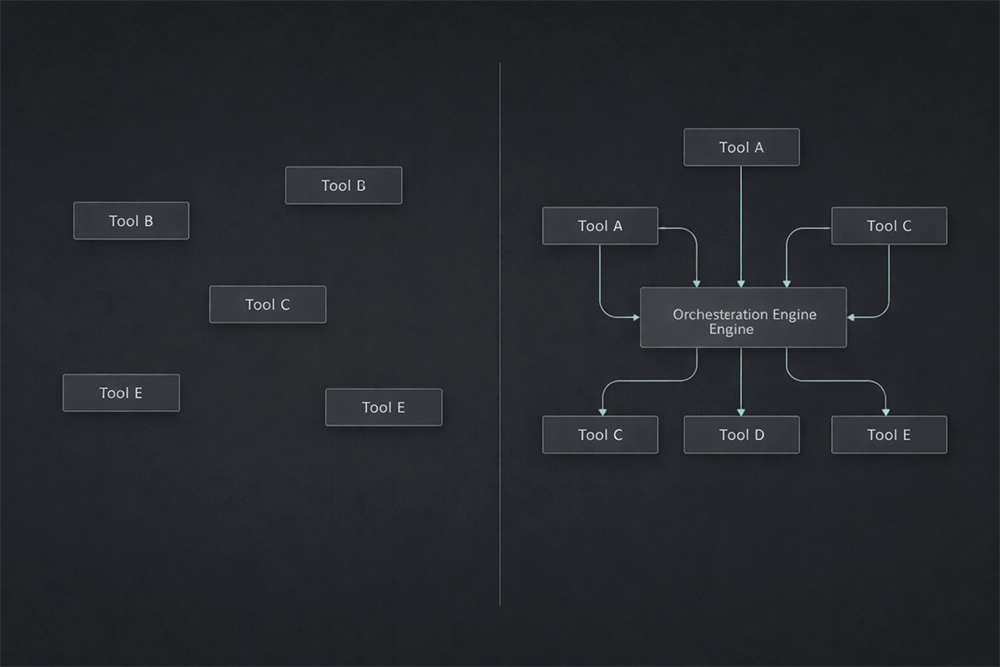
An AI agent in a pentesting workflow should:
Not just summarize.
Not just execute.
But orchestrate.
The difference is architectural.
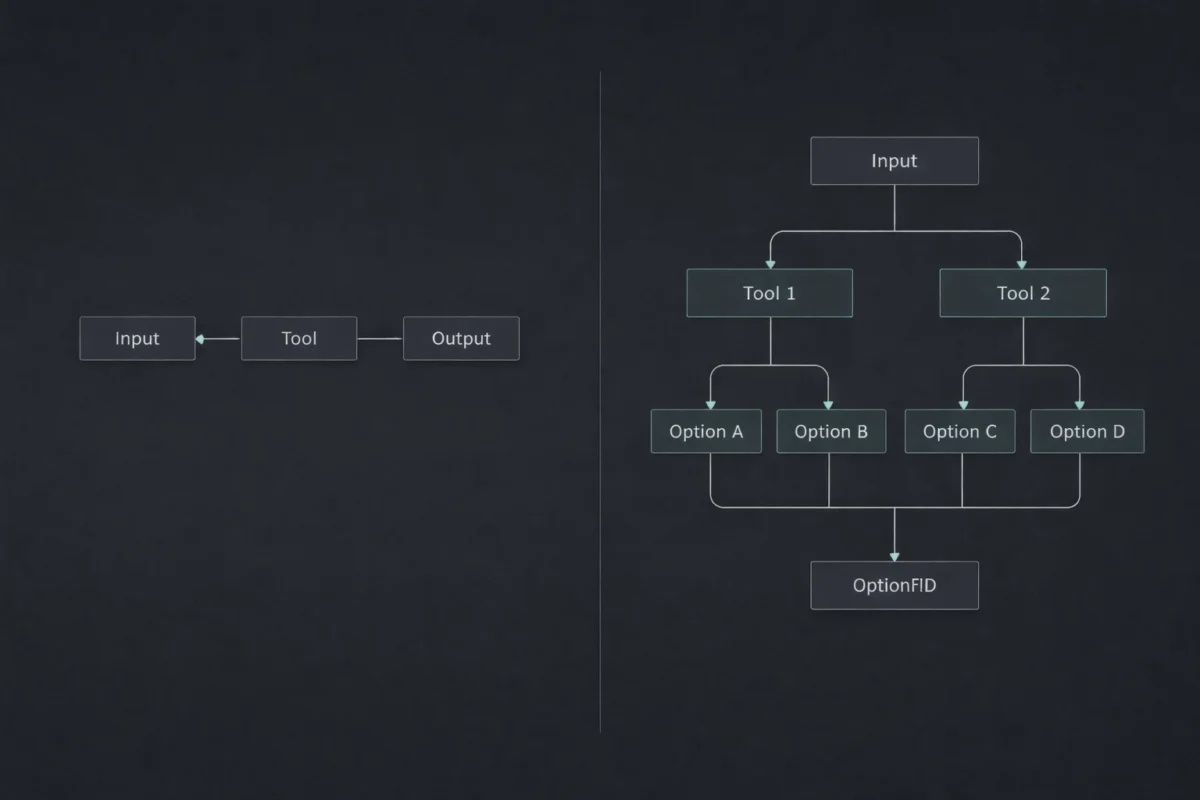
Recon pipelines traditionally look like this:
These tools are powerful.
But they are blind to context.
They do not:
An AI agent with architecture can.
Because architecture introduces:
Recon automation tools are components.
Agents are orchestrators.
Offensive security automation is not:
“Run more tools faster.”
It is:
“How do we structure intelligence across stages?”
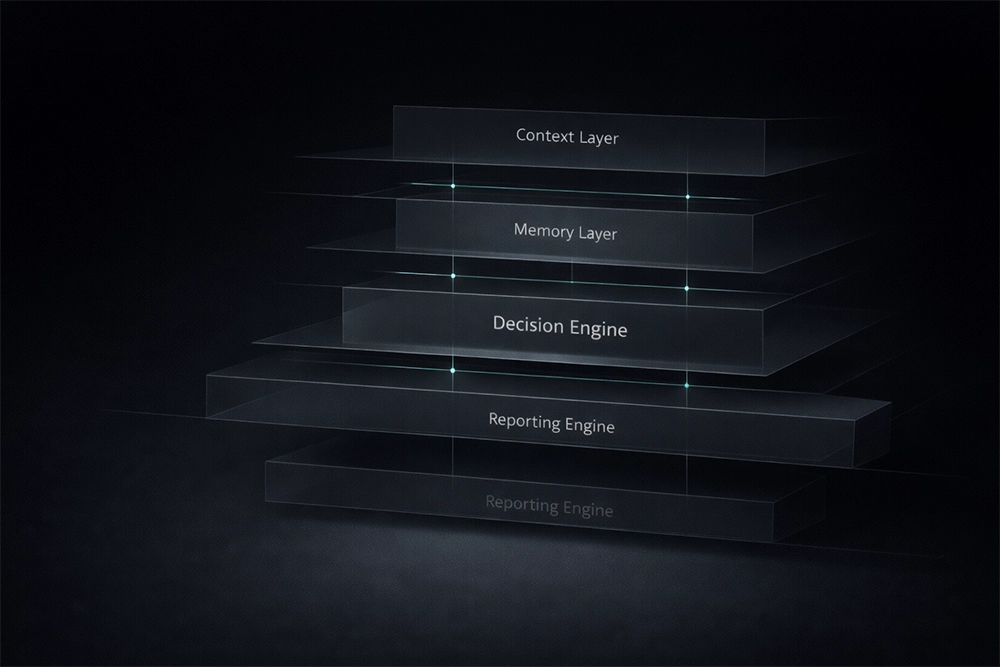
A proper architecture includes:
6.1 Context Layer
Defines:
6.2 Memory Layer
Stores:
Memory prevents repetition.
6.3 Tool Abstraction Layer
Each tool is wrapped in:
Agents should never consume raw CLI output directly.
6.4 Decision Engine
Evaluates:
6.5 Reporting Engine
Produces:
This is offensive security automation with architecture.
Without this structure, AI agents degrade into expensive scripts.
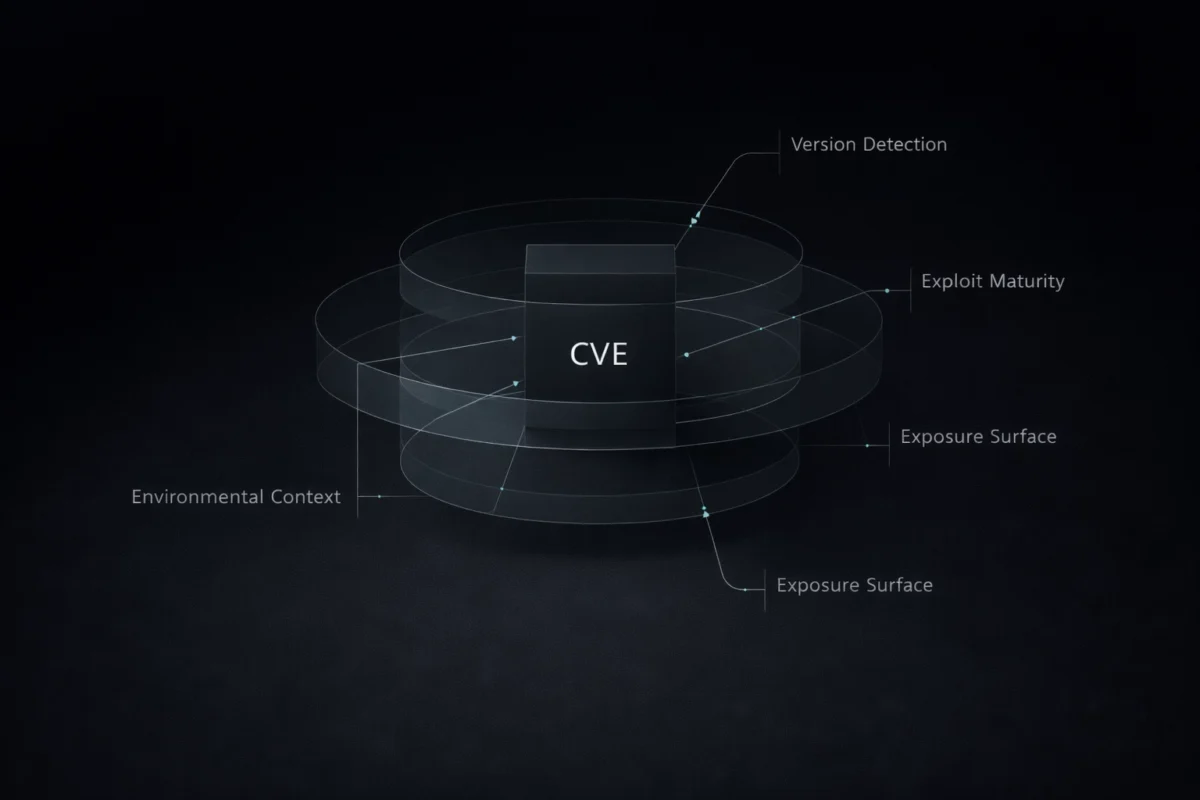
Summarizing CVEs is trivial.
Contextualizing them is not.
An architected AI agent should:
Not:
“CVE-2023-XXXXX is a critical vulnerability allowing RCE.”
Context is what matters.
Architecture allows contextual reasoning.
Common failure patterns:
Agents operate without limits.
Agents hallucinate tool capabilities.
Results become inconsistent.
Agents loop indefinitely.
Architecture solves these.
HEXNULL builds agents with:
Security does not tolerate randomness.
Pentesting is structured thinking.
If AI agents are introduced without structure:
Architecture ensures:
Autonomy must be engineered.
HEXNULL is not building generic AI tools.
The focus is specific:
AI agents for penetration testing workflows.
Current and upcoming systems include:
Each agent is built with:
The goal is not volume.
The goal is precision.
Autonomous systems in security should:
Reduce:
Not replace:
Agents augment.
They do not substitute.
We are moving from:
Tool execution
to
Intelligent orchestration.
From:
Script chaining
to
Agent architecture.
From:
Output aggregation
to
Contextual reasoning systems.
The shift is architectural.
And architecture determines durability.
Autonomous security is inevitable.
But autonomy without architecture is unstable.
HEXNULL exists to build structured AI agents for penetration testing and offensive security automation — engineered systems, not hype-driven wrappers.
If you are a security engineer or pentester looking beyond scripts, beyond dashboards, beyond LLM gimmicks:
Architecture is the next layer.
And it must be deliberate.
Structured AI agents for penetration testing, recon automation tools, and offensive security automation are available for review.

Share:

Introduction Autonomous security is not a feature. It is not a chatbot wrapper around nmap.It is not an LLM summarizing
No account yet?
Create an Account